背景
背景
With the rapid popularization and development of informatization, critical information infrastructure as an important strategic resource related to national security and social stability has become increasingly important
凸显。In order to better respond to cyber intrusions and cyber attacks that threaten critical information infrastructure, implement the "Cyber of the People's Republic of China.
Requirements in the Security Act to improve the protection of critical information infrastructure,Address the needs of regulatory departments such as network information technology, public security, industry security authorities, and network operation departments for Internet asset security situation analysis,The First Research Institute of the Ministry of Public Security designed and developed the "Internet Exposure Asset Risk Dynamic Monitoring System (FD01)".,To comprehensively discover Internet assets, quickly respond to unexpected security incidents, and grasp the security situation of unknown and hidden assets, Establish a comprehensive and efficient Internet asset and risk security monitoring system,Strengthening the protection capability of national critical information infrastructure provides a strong guarantee。

Product and positioning
Internet information, public security and other industry departments
Internet information, public security and other industry departments
A regulatory perspective on critical information infrastructure and key industries。A comprehensive understanding and understanding of the status of network assets in order to quickly respond to issues related to security incidents and form disposal decisions。
Government, ministries and commissions, key enterprises and institutions
Help enterprises and public institutions to manage and monitor key information infrastructure, carry out security emergency response in combination with security incidents, discover and solve problems through asset mapping and analysis in combination with security incidents, promote business development, and form an internal security closed loop
Function and advantage
Asset detection
You can automatically obtain assets and enabled services through various asset collection methods, such as active scanning and traffic monitoring。Identify asset fingerprint information, device type, and manufacturer。
Asset analysis and statistics
Through the tagging management of various asset attribute information and components, it supports advanced asset search and statistical analysis based on each dimension of assets and the scope of vulnerability。Chart types include pie charts, column charts, line charts, maps and other forms。On the basis of preset charts, you can also customize analysis charts based on asset conditions。
Vulnerability scanning and verification
The system presets common and popular vulnerability POCs, and determines the number of assets affected by vulnerabilities based on asset component characteristics.Only threat assets are scanned to improve the efficiency of asset vulnerability scanning and reduce service risks caused by vulnerability scanning。
The violation was discovered
It can automatically discover the devices on the management network that are connected to both the Intranet and the Internet, and report the internal IP address, Internet egress IP address, outgoing time, and accessed Web address of the device。
Security situation analysis [emphasis on description of data mirroring]
Based on the statistical analysis of assets and vulnerabilities, it provides in-depth situational awareness and alarms on asset quantity, distribution, component applications, vulnerabilities, and threat assets to realize security monitoring of assets and vulnerabilities。
Authority control and management
The system supports group management of assets and vulnerabilities。Administrators manage assets under their own accounts based on rights, including reporting and search functions。
Key technology and index
Internet asset discovery technology
Supports scanning detection of known IP assets entry and recommendation of unknown assets based on big data of Internet assets, according to asset clues
(root domain, certificate, ICP, LOGO, key, etc.), regularly automatically recommend and match asset clues with Internet unknown assets
Production, a comprehensive review of corporate Internet network assets。
Rapid scanning technique
Using asynchronous stateless scanning technology, can quickly obtain
Network survival assets can be scanned much faster than traditional ports
A scanner;It is more suitable for enterprises with large assets and
Large-scale network scanning。
Firewall evasion technique
Traditional port scanners open ports to firewalls
There are a lot of false positives, and we have a unique technique
The technique solves the problem of false positives and avoids causing problems to users
Interference improves the accuracy of asset detection results。
Protocol identification technique
Self-developed protocol recognition engine can identify more than 110
A protocol that covers more than 240 common network ports;
The protocol that opens the port can identify and obtain information
(Protocol banner, http header, http body,
Certificate information, etc.), the recognition rate is more than 95%。
Fingerprint recognition technology
Through the self-collected more than 7,000 fingerprint rules, the asset label management;Fingerprint covers a variety of network management products/components for quick integration
Measure the coverage and usage of a business application。
Multi-engine vulnerability scanning technology
The combination of asset fingerprint-based POC scanning engine and Web special scanning engine can meet various fields such as comprehensive risk security detection and special detection of sudden vulnerability events
Quickly and accurately locate risks。
Asset discovery
Combine the input of known assets with the recommendation of unknown Internet assets based on big data of Internet assets to comprehensively sort out the Internet network assets of enterprises;
Support based on the configuration of Internet asset clues (such as domain name, certificate, ICP, LOGO, keyword),
Automatically recommend Internet assets on a regular basis;
Port scanning
Supports full-port scanning, such as http port 443, telnet port 23, and windows remote connection
Such as 3389, and supports user-defined port addition。
Scan 10000 assets. 5M bandwidth for all ports for 30 minutes。
Protocol identification
Support more than 200 mainstream protocol identification, including application layer protocol, network layer protocol, industrial control protocol identification
(CoDeSys, GE-SRTP, SIEMENS, MELSEC-Q, omron, etc.)。
Rule recognition
Supports asset labeling group management, and can customize multiple asset attribute labels based on enterprise services.
Over 7,000 fingerprint recognition rules。
Supports rule classification management, and you can add custom rules。
Vulnerability scan
The system presets a rich vulnerability POC library and supports special vulnerability scanning based on asset fingerprint matching PoC。
The preset Web specific scanning engine supports specific and deep vulnerability scanning for Web applications
Supports automatic scanning policies to periodically check and alert assets。
Products and services
FD01 public cloud support service
FD01 Public cloud network space mapping big data support
FD01 public cloud cyberspace mapping system can continuously detect IP addresses of the whole network, perceive and update various assets and states in cyberspace in real time, and provide the latest, most complete and accurate big data of Internet assets for FD01 products。
Product rule update support services
Asset fingerprint collection and update
Development professionals provide assistance in adding protocols, non-standard ports, and custom rules based on enterprise assets。Customized according to customer assets。
Vulnerability POC support service
Professional vulnerability analysis and discovery team, dedicated to vulnerability discovery research。Organize tens of thousands of white hats, collect the latest threat intelligence information, the first warning。
Questions and Answers
What are the features of FD01?
FD01 is mainly based on the function scenario of Internet asset discovery and risk monitoring。
"Known" asset management and "unknown" asset recommendation based on Internet asset big data。
POC scanning +Web special scanning based on asset fingerprints, fully covering all types of Internet asset risk investigation and sudden vulnerability emergency scenarios。Periodic asset and risk security monitoring to monitor new Internet unknown assets, asset changes to known assets, new vulnerabilities and risks。
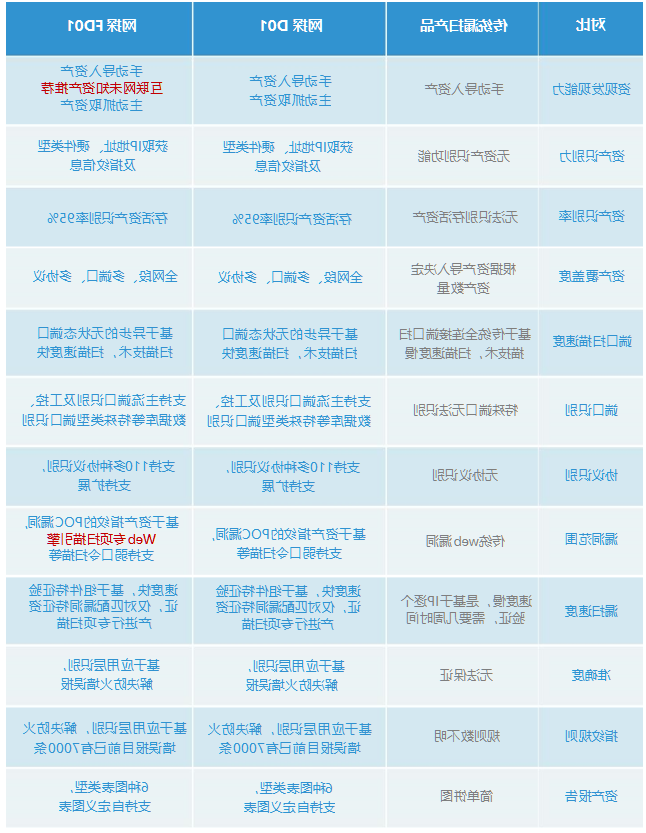
The difference between FD01 and traditional scanner and D01?
Advantages compared with similar products?
Functional advantages: comprehensive, fast, accurate and timely
Asset discovery: The system supports manual input of known assets + Internet unknown asset recommendation based on asset clues (such as domain name, certificate, ICP, LOGO, keyword), so that the Internet invisible assets have nowhere to hide, leaving no management blind spots。
Asset search: support fuzzy search for assets;Advanced search by asset IP address, asset name, port, service, operating system, device type, vendor, component, device region, company, management group, and service application。
Port scanning: Support IP port scanning, depth identification of more than 240 commonly used network ports, including the default and non-default ports of the protocol, and support for custom ports。
Protocol identification: Support more than 110 kinds of mainstream protocol identification, including database, SSH, FTP, HTTP, program components, industrial control and other types;Support protocol extension。
Fingerprint recognition: Preset more than 7,000 fingerprint recognition rules, including video surveillance, security products, routers, switches, OA, finance, mail, project management, etc。
Scanning speed: 10000 assets can be scanned, 240 common network ports (5M bandwidth for 30 minutes)。
High accuracy: It can accurately identify the open condition of the protocol, and the false positive rate due to connection reset and firewall is less than 3%。
Vulnerability scanning: The system supports various scanning scenarios, such as asset fingerprint-based vulnerability POC scanning and Web-based special scanning, and is suitable for various scenarios, such as comprehensive asset vulnerability scanning and burst vulnerability POC special scanning。
Analysis report: including asset analysis, vulnerability analysis;Conduct statistical analysis on the changes of the asset's device type, manufacturer, port, operating system, database usage, regional distribution, and total assets;The distribution and impact of vulnerabilities are analyzed statistically.Support pie chart, column chart, line chart, map and other chart forms;Support for adding custom charts。
How can vulnerability POC be continuously protected?
A team of professional security engineers output hot and latest vulnerability POC every week to quickly respond to sudden security incidents。
How to respond to equipment upgrades and maintenance?
Update the functions and vulnerabilities of the equipment, set up a localized service organization, and ensure that the door is open within 4 hours。
Application scenario
Platform level system
It is suitable for industry supervision units and group-level units to build industry-level and group-level comprehensive monitoring and situational awareness solutions for Internet exposed assets and risks;
Rack-mounted system (Soft deployment)
It is suitable for the deployment and use of units with large Internet exposure, to discover hidden Internet assets and risk monitoring, and to establish a normal Internet assets and risk monitoring mechanism。
Portable tool kit
Applicable to the network security check between superiors and subordinates, it can quickly and comprehensively discover asset exposure and security risks, and automatically generate reports。